Swiss Cyber Storm write-up 3: Social Challenge
This long delayed article is a write-up of the Swiss Cyber Storm Social Challenge which took place on May 14, 2011. Because of lack of time I simply did not finish this article earlier, however since I really enjoyed the challenge I decided to release it anyways, even though it is a bit dated now.
For more info on the Swiss Cyber Storm Conference please check my post about the conference here.
The number and title of this challenge were:
- 7038 HackNight Challenge
The description on the website of this challenge was:
First of all, we won’t tell you any details about this challenge. But be sure you won’t miss the HackNight Party.
You can gain another 20 points and let your competitors behind you!
[https://www.hacking-lab.com/cases/7038-hacknight/index.html]
Challenge
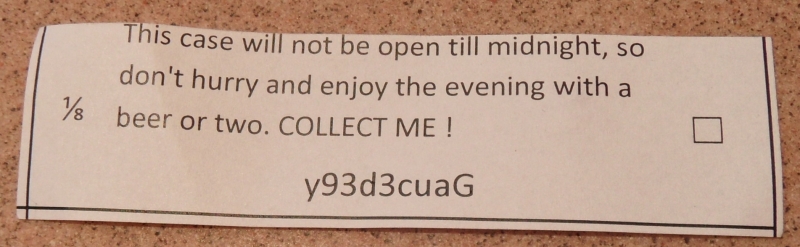
During the ‘HackNight Party’ you would receive strange pieces of paper with each beer you would order. Knowing about the challenge this of course triggered us to look into these pieces of paper. Since this challenge was a social challenge I did not do this challenge on my own, but did it partly together with Peter “pesche”. One of the pieces of paper you would receive is shown below.
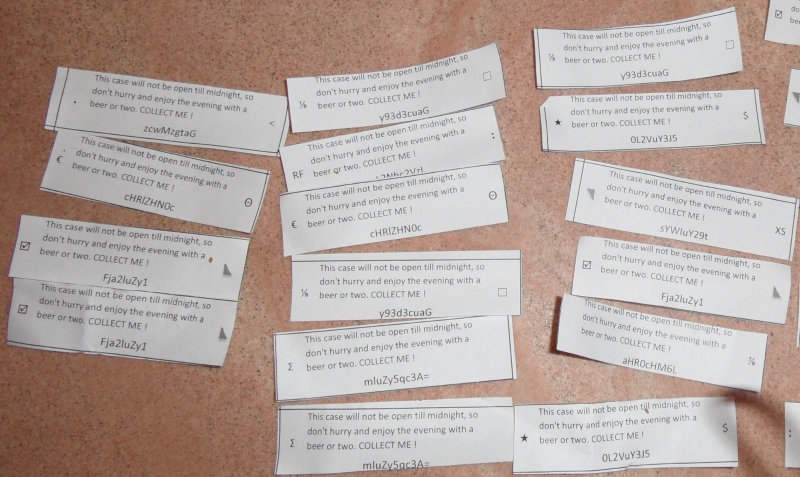
So, we had a piece of paper with the text “This case will not be open till midnight, so don’t hurry and enjoy the evening with a beer or two. COLLECT ME !“, with below it a seemingly random string and two strange characters on the sides. Since we couldn’t do much with one piece of paper we followed the advise on the paper and enjoyed a beer or two. This did give us some more pieces of paper, but not a lot more info. Since we were not with a big group and didn’t want to drink 30 beers each we decided to play this game a bit differently from the other players. Although this was designed as a social challenge, most people did not want to share their pieces of paper, however they did all lay them out on the table to study them. So instead of gathering the pieces of paper we came up with the approach to make pictures from the pieces of papers on the different tables. We only had a couple of pieces of paper ourselves in the beginning but were able to solve the whole challenge using the camera approach. One of the pictures showing quite some of the pieces of paper is shown below.
With analyzing the pieces of paper we figured out the idea behind the challenge, the seemingly random characters on the sides of the paper could be used to link the pieces together.
Some examples:
- 1/8 and 7/8
- XS and RF
- $ and €
Some of the pairs were more obvious than others, but we figured out the full link of paper pieces. Both the first and last pieces of paper only had one character, clearly showing that they were the end points. After combining the pieces of paper we combined the random strings at the bottom together, which led to the following combined string:
 aHR0cHM6Ly93d3cuaGFja2luZy1sYWIuY29tL2Nhc2VzLzcwMzgtaGFja25pZ2h0L2VuY3J5cHRlZHN0cmluZy5qc3A=
The characters in this string and the = on the end quickly gave us the idea that this might be a base64 string.
Converting base64 to plain-text can be done in multiple ways, one way to do the decoding is using the base64 tool on Linux:
root@bt:~# echo "aHR0cHM6Ly93d3cuaGFja2luZy1sYWIuY29tL2Nhc2VzLzcwMzgtaGFja25pZ2h0L2VuY3J5cHRlZHN0cmluZy5qc3A=" | base64 -d https://www.hacking-lab.com/cases/7038-hacknight/encryptedstring.jsp
Other ways to decode base64 is to use online tools such as this one.
After decoding the base64 string we ended up with the following url:
- https://www.hacking-lab.com/cases/7038-hacknight/encryptedstring.jsp
Like the pieces of paper stated the website would not show anything till 0:00 at night, so there was no other option than to take some more beers and wait.
After 0:00 and back in the hotel I decided to check the website again to see what it would come up with. When visiting the website a seemingly random piece of text showed up, so the challenge was not solved by just visiting the website. The text that showed up is shown below.
Yvv iigl hk hyx zvkaysfna zeg ng sxarx hs oce avhxx pp mpr mgnelbbvil tt kam fiekwja iah mms krznrgd cw xdvp fjb. Semfwxi wj am jlh, nb kam aefj cw vpnvbym rgl tshi kzet, flxuvvklf xaj kvts glktixa bui ofzcxg bj wffbgmfw, ytf yx qf xkzzp aqf fkthyxz’f oxjdvk iah mms wbvqik tt chag ganzukma. Egi W nbty wmwwbx lbag zdfg buix bwka oeity jvgoreghs rgl sykncll iakxw hyhar aat kfntq emysdib gs itwjhv nrw isjmzbc Fd pihbuikx. Oew gby pnzc dvba Fd brfm vw mms Chzq aajb Z eil Qr asezmnrvj ighv glxj.
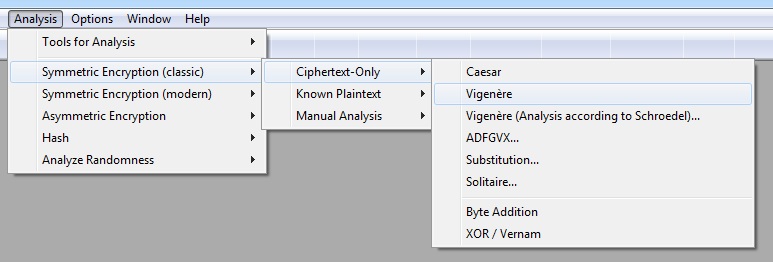
The text seems to be an encrypted message, since I had no idea what the crypto algorithm might have been I decided to use Cryptool to get some more info on it. Cryptool has a lot of options, including analysis tools to figure out what kind of encryption was used and how it might be decoded. Within the different analysis options there is the Vigenère cipher.
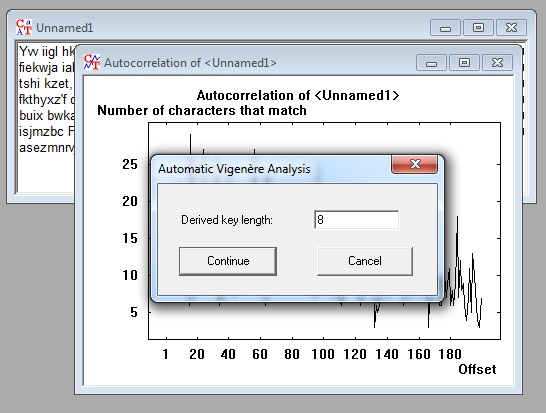
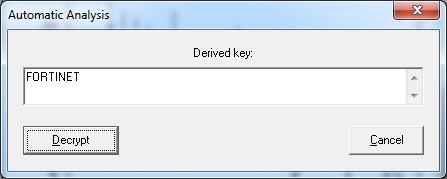
Cryptool seems to recognize the encrypted text as being encrypted with the Vigenère cipher and Cryptool is even able to analyse the encrypted text to figure out the encryption key.
More information on the Vigenère cipher can be found here: http://en.wikipedia.org/wiki/Vigen%C3%A8re_cipher
Cryptool shows us that the key to decode this encrypted data likely is “FORTINET” as can be seen in the screenshot below.
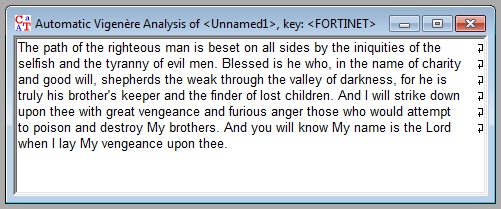
Fortinet was one of the sponsors of the Swiss Cyber Storm conference. When we decrypt the data with Cryptool using the key we found we find the following plaintext text:
The path of the righteous man is beset on all sides by the iniquities of the selfish and the tyranny of evil men. Blessed is he who, in the name of charity and good will, shepherds the weak through the valley of darkness, for he is truly his brother’s keeper and the finder of lost children. And I will strike down upon thee with great vengeance and furious anger those who would attempt to poison and destroy My brothers. And you will know My name is the Lord when I lay My vengeance upon thee.
Which seems to be a quote from the movie Pulp Fiction where it is referenced as a bible quote.
I submitted the decoded text, the key and that the quote comes from Pulp Fiction as my answer and it was accepted by the jury, after which I finally could get some rest which was well deserved after all the beer drinking 😉

Leave a Reply